-
Introduction
Today’s internet ecosystem challenges users’ privacy, security and anonymity as more business models monetize personal data. A variety of tools exist claiming to better protect users online by cloaking or redirecting their browsing from would-be trackers and throttlers. Among the most common solutions is the Virtual Private Network(VPN) alongside lesser utilized proxy servers and the question of how the technologies differ.
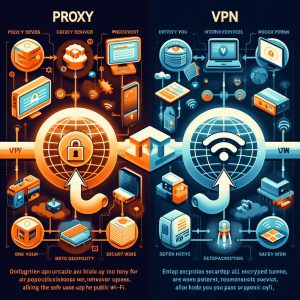
Both proxies and VPNs funnel internet traffic through alternative servers for additional layers of privacy or optimized routing. They share certain functionalities on the surface but take vastly divergent approaches under the hood influencing security, reliability plus ease-of-use. Evaluating where each option succeeds and falls short helps match users with the right tool given their priorities.

-
What is a Proxy Server?
A proxy server acts as an intermediary relay situated between endpoint devices, like computers, and wider networks such as the web. Essentially it functions as a gateway that browsing sessions must pass through before connecting to intended websites and services by routing traffic through the proxy server first before reaching destinations. These jump points link internal local area networks like a business or university’s systems to external networks providing administrative control and monitoring.
Proxy servers operate on the logic of masking the originating computer or device’s source IP address by assigning an intermediate one for sites on the other end of the connection to perceive instead, which adds an element of privacy and anonymity. The 2 main types include web proxies which specifically handle web browser traffic in addition to general purpose transparent proxies for entire networks. Administrators customize access policies and traffic filters as needed when serving say a school or workplace.
Benefits proxy servers bring to the table primarily include ability to hide the real IP addresses and systems users operate from along with their physical locations. This can facilitate anonymity goals without full attribution or inhibit surveillance efforts profiling individuals. Proxies also enable circumventing blocks or filters by accessing blocked materials re-routed through servers elsewhere without restrictions. They work adequately for simple webpage access and concealing immediate origin points as intermediary stepping stones to wider internet destinations. However their capabilities remain quite limited next to full VPN functionality.

-
What is a VPN?
VPN is short for Virtual Private Network and similarly obscures internet traffic by funneling it through remote server networks. But unlike proxy servers that mainly only supply alternative IP addresses then directly shuttle data to websites relatively unencrypted, VPNs built entire multi-layered tunnels comprised of protocols securing end-to-end data flows.
The core technology enabling VPN connections involves encryption through protocols like OpenVPN or IPSec which package up device traffic entering the VPN server network, lock it behind multi-factor authentication systems using digital certificates between client apps and networks, then transport wrapped contents securely across intermediary servers and routers until reaching the exit node destination. Only there does decryption unlock the user’s traffic, typically assigning a new IP, before routing it the last mile through conventional internet channels.
This creates an encoded tunnel protecting the entire transit regardless of what applications generate the data, whether general browsing, streaming video platforms or BitTorrent clients. Moreover VPN encryption exceeds normal HTTPS protocols shielding communication contents not just securing the transport layer transmissions. Many services add extra conversions using the highest-grade AES-256 bit and 2048 RSA encryption plus features like shared IP addresses among users or AirVPN’s multi-hop routing bouncing between layered VPN servers for extreme privacy.
As a result, VPN capabilities outclass proxies substantially regarding security, anonymity plus ability to bypass internet filters and geo-blocks censoring content like streaming media subscriptions limited to certain regions. The encryption applied universally across apps and whole operating systems also fixes issues leaking identifying DNS data that partially undermines protections at the web traffic layer alone. For the ultimate in anonymization and data safety, VPNs lead against basic proxies.
-
Key Differences
While proxies and VPNs both reroute internet activity in ways aiming to enhance privacy and access controls, thediaverge considerably in their implementation and effectiveness:
Security – VPNs encrypt 100% of device traffic always securing data flows universally across networks for robust layered protection leveraging highest-strength cryptographic algorithms. Proxies have zero encryption applied by design, only altering IP addresses then shuttling unprotected payloads the remaining distance.
Anonymity – Because VPN encryption and rerouting works intrinsically across apps and devices rather than just anonymous IP addresses on web traffic, VPN defeats surveillance efforts tracking unique device fingerprints comprised of data like hardware info, cookies and browser settings. Proxies expose these identifiers allowing persistent monitoring.
Coverage – Whereas proxies exclusively focus obfuscating web browsing to varying degrees, VPN encryption encapsulates all network data traffic regardless of its origin or destination app – from web services to gaming, P2P sharing or IoT device telemetry benefiting from processing privacy too. Proxies miss major vulnerabilities.
Reliability – Due to lacking meaningful encryption itself, proxies depend wholly on nearby single intermediary jump points between devices and websites targeted. Any disruption breaks this delicate chain. VPN encrypted tunnels better withstand intermittent network dips or blocking attempts by weaving through server mesh networks with smart rerouting redundancy. Proxies break more easily when pressured or blocked because simpler linear architecture affords no failover or comeback workarounds to rely messages mid-transit as VPNs innate capacity for multi-routing lends.
-
When to Use Proxy vs VPN
Proxies work reasonably well for extremely basic privacy goals around hiding immediate public IP addresses visible when accessing plain webpages. Students in restrictive networks aiming to bypass filters on sites or specific pages can leverage proxies as temporary secrecy measures given their lesser visibility to network admins auditing traffic compared to app VPNs which universally alter traffic profiles.
However VPNs outclass proxies substantially for robust reliable security, future-proof capacity allowing encrypted support across modern apps and protocols – not just retrofitted webpage browsing – plus unlocking geo-restricted content and blocked communications channels abroad where deep packet inspection foils lesser forms of traffic obfuscation outdated proxies employ.
Ultimately the split depends whether users prioritize surface-level obscurity temporarily guarding just URLs visited or complete enclosed transport privacy across entire devices and operating systems through hardened end-to-end encryption with award-winning protocols like OpenVPN, WireGuard and AES-256 bit protection tested reliable for decades. Casual final mile browser privacy alone defers to barebones proxies while universal network-wide encryption requires premium VPNs up to speed on innovations like perfect forward secrecy, split-tunneling and trusted audited infrastructure.
-
Conclusion
Online privacy, security and censorship circumvention fundamentals increasingly shift towards solutions like Virtual Private Networks able to encrypt blanket traffic through robust authenticated channels rather than legacy proxy servers limited to superficial IP address anonymization lacking durable multilayered protections fit for securing complete transport security across apps, systems and data types.
VPNs lead decisively on fronts like encryption depth, scope platform support plus advanced traffic analysis resistance and filter evasion precisely due to bespoke protocol innovation dedicated purely to hardening network security assurances through earned customer trust. Meanwhile aging proxification satisfied rudimentary webpage privacy years ago but failed modernizing assurances , fidelity responding to threats far outpaced by VPN versatility traversing the core privacy fault lines overlooked leaving users highly vulnerable by clinging to narrow outdated use cases.
In time aging stopgaps like insecure proxies lingering in narrow legacy duties will continue ceding ground to complete traffic tunneling solutions prioritizing user-first design excellence through R&D investments committed keeping customers shielded. Discerning users should weigh particular application needs but understand complete device coverage and futureproofing trends toward total end-to-end network privacy where VPN solution extensive advantages shine leaving limited proxies relics abandoned except extremely narrow use case exceptions. Total device coverage and futureproofing trends toward total transport-layer privacy solutions where VPN extensive advantages shine.